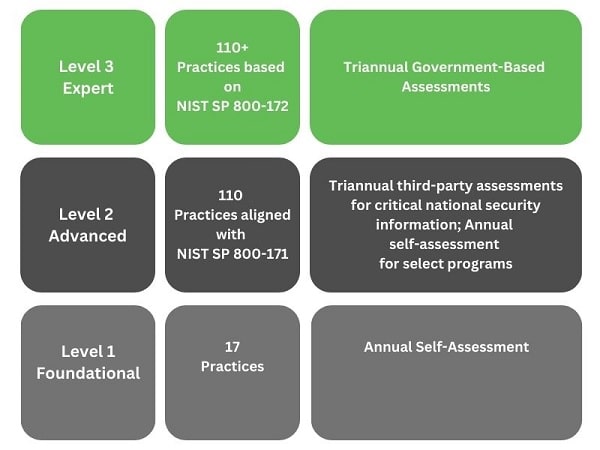
2023 Update: Since the publication of this article, the Department of Defense has announced the updated requirements of CMMC 2.0. Under this new version of the model, Level 1 contractors no longer require third-party assessment. Instead, Level 1 contractors must submit an annual self-assessment with affirmation from company leadership. Learn more about CMMC 2.0.
CMMC Level 1
Audits will soon begin for Cybersecurity Maturity Model Certification or CMMC. If you’re a Department of Defense contractor, you will need at least CMMC Level 1 to keep your place in the Defense Industrial Base. So where should you begin?
If you’ve worked with the DoD before, your contract has likely contained some level of cybersecurity compliance. But until now, your contract hasn’t required a formal certification.
Under previous regulations, contractors could get by without meeting all the cybersecurity requirements in their contracts. Some contractors simply didn’t have the time or budget to meet requirements that wouldn’t be audited. Others didn’t even notice the cybersecurity language buried in the fine print. But now, with formal certification looming, many businesses find themselves rushing to catch up.
Here’s the good news: We’re still in the early stages of CMMC. Audits are expected to begin this fall and will roll out completely over the next five years. That means it’s not too late to get a jump start on CMMC. You can start preparing right now.
At Core, we’ve already helped nearly a hundred companies prepare for CMMC Level 1. Even if your business requires Level 3, this first level is an essential step.
Here are our tips to prepare for CMMC Level 1:
Preparing for CMMC Level 1
1. Learn the requirements and conduct an assessment
To start, learn the actual requirements of CMMC. What are the 17 practices required for this level? What technologies, procedures, policies, and training are needed? Which requirements do you already meet, and where do you need to improve?
Some practical steps to get started: Visit the DoD website to download the actual CMMC model. Look for the 17 practices of Level 1 and review them with your IT and management teams.

Wading through these technical requirements might feel like a chore. Who likes to read government documents? Now, add cybersecurity jargon to the mix. On top of that, each requirement is a single sentence with little explanation.
That’s one reason we suggest training as part of this first step. Without expert guidance, it’s easy to misunderstand or misapply these requirements. Good training will save you time and money in the long run.
Once you’ve reviewed the practices of CMMC Level 1, perform an assessment. You might already meet some of the requirements. But what about the areas where you fall short? Make a list of gaps in your current IT and business practices.
Then it’s time to plan. Build a technology roadmap; what upgrades, changes, and new technologies do you need to meet the requirements? How will you implement those changes? And what’s your budget for the project?
2. Implementation and Remediation
Previous cybersecurity regulations have allowed businesses to submit a “Plan of Action” to cover the requirements they miss. But under CMMC, your auditor will want to see that you’re practicing the standard. That means it’s time to implement your plan.
This involves remediation. Remediation simply means making changes and improvements to your network and devices, “remedying” potential security flaws.

This is also where you will write any needed policies and procedures. Documentation matters much more for CMMC Level 3 and above, but some are still required for Level 1.
Wisdom from ISO: In addition to CMMC, we help hundreds of small businesses implement ISO 9001 and related standards. ISO requires periodic management review meetings, and we highly recommend the same for CMMC. Hold regular meetings with management and business owners to check status, set direction, and evaluate roadblocks. This is a great way to involve leadership and keep your project on track.
3. Third-Party Certification
Once you’ve implemented the requirements of CMMC Level 1, you’re ready for the audit. This audit will be performed by a third-party registrar certified by the CMMC Accreditation Board.
Again, the DoD has until 2026 to roll out CMMC for all its contracts. Your audit might not take place until next year or even later. But be prepared: once the audits begin, they will happen quickly, and the requirements could grow significantly as the first audits are completed.

Wisdom from ISO: ISO standards require an internal audit, and we highly recommend doing the same for CMMC. To best prepare for your final audit, perform your own audit in-house to catch existing problems. It’s much better to catch and fix these now, internally, than later during your final assessment.
After the assessment, you might need to make some corrections. You’ll have a 90-day window to fix any problems, after which you receive your certification. This certification lasts for three years.
But that’s not an invitation to stop thinking about cybersecurity. Security remains paramount, especially when working with government information that could attract cyber threats. The processes of CMMC Level 1 can help you maintain basic cyber hygiene even outside of DoD contracting. And when recertification rolls around, your auditor will want to know you’re still following CMMC practices.
How much time will this take? Allow for several months of preparation. This isn’t something you can knock out a couple of weeks before the audit. CMMC auditors receive extensive training and are held to a high standard. They can’t cut corners, so neither can you. To pass this test, you need a score of 100%. Preparation time is the key to success.
How Core Can Help:
At Core, we specialize in helping American small businesses achieve cybersecurity. We provide training, gap assessments, and technical solutions to take the “guesswork” out of CMMC prep. As a Registered Provider Organization with the CMMC Accreditation Board (CMMC-AB), we are an officially recognized source of CMMC consulting and solutions. We also have several CMMC-AB Registered Practitioners on our consulting staff, specifically trained to help businesses like yours implement CMMC.

Here’s a look at how Core Business Solutions can help:
- Our Registered Practitioner consultants help you learn the requirements of CMMC and apply them to your specific context.
- We provide online training for your leadership, staff, and IT professionals.
- We deliver the technical security solutions required for certification, such as vulnerability scanning and management. We’re in the process of rolling out even more solutions, including email security and penetration testing.
- We assist your company in preparation for the third-party certification audit.
It’s not too late to get a jump start on CMMC Level 1. By starting now, you can ensure cybersecurity success in the future. Learn more at our CMMC page or get a free quote.




